Visualization of the classification of technical means of telecommunication systems.
Introduction
The purpose of a telecommunication system is to exchange information between users of the system. This information exchange can be carried out in various ways, for example, through multiparty voice communication, television, e-mail and electronic messaging.
The worldwide telecommunications infrastructure in 2001 consisted primarily of two interconnected core infrastructures: the telephone network, which is a circuit-switched network, and the Internet, which is a packet-switched computer communications network.
Today, the telephone network is managed mainly through computer communication networks, and the means of transmission that connect the main components of the Internet are derived from the same means that connect telephone switches. The current state of the art today is the result of a huge increase in scientific knowledge and significant advances in a wide range of technologies over the past two centuries. Indeed, it is not easy to identify areas of science and technology that do not have a certain impact on the current state of telecommunications. Thus, any brief discussion of telecommunications should, of necessity, omit significant parts of the story.
The purpose of the work: Visualization of the classification of technical means of telecommunication systems.
Work tasks:
1. Describe the theoretical information about telecommunication networks.
2. To study the technical aspects of designing telecommunication networks.
In this article we will use SNgrep to visualize or analyze the traffic of a telecommunication network.
- CLASSIFICATION OF TELECOMMUNICATION SYSTEMS
1.1 Types of telecommunications systems
Telecommunication systems include wired and wireless local and global networks, as well as hardware and software that enable systems to interact with each other or with users. The set of telecommunications systems that support most federal government agencies includes network infrastructure and other solution components owned by commercial telecommunications service providers and managed on behalf of the government. Dependence on telecommunications system providers presents system owners with specific contingency planning issues that the ISCP must decide, such as whether the same or another provider will be responsible for providing alternative telecommunications services if the primary service becomes unavailable. Contingency planning strategies for telecommunications systems include:
- Using the results of business impact analysis to determine contingency requirements for maintaining or restoring telecommunications services.
- Documentation of telecommunications infrastructure and services with physical and logical network or architectural diagrams.
- Documentation of system configuration information, names and contact information of telecommunications service providers, as well as service level agreements in case of unforeseen circumstances.
- Aligning contingency solutions with network security policies and security controls to provide adequate protection against network outages or other failures.
Contingency planning for telecommunications systems should aim to avoid single points of failure by implementing redundant links, network devices, and even service providers. In addition to network and provider redundancy, the capabilities provided by telecommunications systems for normal operation can provide contingency solutions when primary processing centers or supporting infrastructure components are unavailable. These capabilities include remote access services for system administrators and other authorized personnel, as well as wireless network technologies as an alternative or backup mechanism for communications during disruptions affecting the LAN or other wired network components.
UMTS is a mobile system with a maximum downlink speed of 384 kbps and a maximum uplink speed of 128 kbps. It is the successor to GSM, based on 2G networks, offering only phone calls and small amounts of data through the MMS service. In fact, UMTS, which represents the core 3G wireless technology, offers wireless Internet access services on a global scale, expanding the capabilities of 2G wireless networks from simple voice telephony to complex data applications, including Voice over Internet Protocol (IP), video conferencing over IP , web browsing, multimedia services and high-speed data transmission [7]. Therefore, once the 3G system took over the market in 2003, it offered more data, such as video, and a wider range of extremely advanced services, allowing the new ubiquitous technology to surpass previous ones. A variant of UMTS Time Division Duplex (TDD) called Synchronous Time Division Code Division Multiple Access (TD-SCDMA) is also standardized by 3GPP. The technology operates in a 1.28 MHz bandwidth and is mainly deployed in China.
The Universal Mobile Telecommunications System (UMTS) has played an important role in the development of new third generation products and standards for the future public land mobile communications. There were four dominant types of mobile systems (especially in Europe), including:
1.Cellular systems based on Global System for Mobile Communications (GSM) adapted from the Second Generation Pan-European Digital Mobile System.
2. Wireless systems based on European digital wireless telecommunications are also referred to as “CT2” for “second generation cordless phone” and “CT3” for “third generation cordless phone”.
3. Paging systems based on European means of radio messaging.
4. Private mobile radio systems in the United Kingdom.
The European Community has organized its 3G wireless efforts under the umbrella of Research and Development for Advanced Communications in Europe (RACE). The efforts of the RACE-1 project in Europe are concentrated in eight main areas:
1. fixed network and its functional characteristics,
2. mobile systems and services,
3. alignment,
4. modulation and coding,
5. channel and cellular management,
6. signal processing in mobile communication,
7. broadband mobile systems,
8. other related technologies such as antenna design in relation to the CT3 band.
As a continuation, the RACE-2 project was launched. This project focuses on implementing 3G systems and organizing their operation in a top-down, feature-oriented way that ensures system specification meets requirements and technical support is available for CT3 mobile systems and products.
UMTS provides bearer services as defined in the context of GSM and ISDN. These “bearer” services may be circuit-switched or packet-switched. ISDN supplementary services are likely to be supported by UMTS. As mobile telephony begins to gain popularity, 8, 16 and 32 kbps and unrestricted B2 channel services are likely to become part of UMTS. Applications for new wireless services can be very diverse, such as low bit rate video, image search, audiovisual services (but not multimedia), videotelephony, and so on.
In theory, most of these systems have an air interface with each other, since they cover the “last few miles of wireless communication” to serve the mobile user. From this air-interface network access point, access to other existing networks, DCPN, BCPN, MCPN, or public UMTS networks, can be made over any of the media such as fiber, coax, microwave, or even twisted pairs in ADSL/ HDSL1 (ITU G.992.5, 2009).
The use of advanced telecommunications systems will increase. This includes next generation wireless and RF technologies, Voice over Internet Protocol and the use of hardware devices such as personal digital assistants (PDAs). Libraries for health and health sciences have already adopted and integrated PDA technology with some library services.
Syndication of information, new product packages and the development of vertical portals (called vortals) seem to be on the rise. Syndicated electronic content means that the same content is packaged and sold through multiple portals. Vortals typically bring together e-commerce, software applications, trade news, and content. All of them are delivered to the user for a fee. Academic market vendors model some products this way by providing specialized research portals. One example is Ovid On Call from Ovid Technologies, which provides a portal to access medical and healthcare resources. Current usage of website/database home page customization and personalization may also increase. Libraries and users may find a selection of frequently used resources, references and databases a more efficient approach to research. Of course, as universal search and automatic categorization of websites improves, this may no longer be necessary.
The internationalization, multilingual access, and translation functions of library information systems will become more viable through international alliances, programs, and standards that facilitate the translation of documents.
E-books are still in the early stages of development. For e-books to become a viable, mainstream and modern information technology, e-book makers will need to develop and implement better standardization and features that will make reading on the web suitable for more than brief reference use.
Interaction and interconnection between information sources will increase and improve with the use of OpenURL, the Open Archives Initiative (OAI) and XML. Several major libraries (National Library of Medicine and NASA Astrophysical Data System) have chosen the XML format (Miller). XMLMARC is under development and XML is being integrated into ILS and commercial information databases.
1.2 Advantages and disadvantages of Fiber Optic Link
Fiber optics is a technology used in wired digital communications. Also known as optical fiber communication, it involves the transmission of data in the form of pulses of light over thinly stretched or stretched glass or plastic called optical fibre.
The use of optical fiber for wired digital communications is preferred over electrical cables or copper wires due to numerous benefits. It is also important to highlight the fact that the benefits of optical fiber derive from the benefits of optical fiber. Thus, optical fiber is a more advanced form of digital communication than electrical transmission.
Advantages of fiber optics:
1. Suitable for high bandwidth applications
The most notable benefit of fiber optics is higher bandwidth digital communications than copper wires, enabling faster data transmission and complementing wireless communications technologies. But why does fiber optic technology have a higher bandwidth than electrical transmission? The simplest explanation is based on a property of light.
Power transmission systems based on copper or other metals transmit data in the form of electrical currents. An optical fiber sends data in the form of light pulses. Note that light is a very high frequency signal. This means that the optical fiber can transmit a higher frequency range. The higher the frequency range, the higher the bandwidth.
2. Provides long distance transmission and communication
Fiber optics is also suitable for transmission over longer distances than today’s copper lines because it exhibits minimal attenuation loss. Current generations of fiber optic systems have attenuation losses as low as 0.2 dB/km. This allows long distance transmission with little or no need for signal repeaters. Optical fiber can travel over 100 kilometers without active or passive processing.
On the other hand, copper wiring suffers from losses due to its electrical properties, requiring built-in signal repeaters every couple of kilometers. For example, when signals travel down a copper wire, it loses some of its energy. Resistance contributes to the loss of energy and even more so. The longer the cable, the more resistance it provides. Also, copper wire loses signal power at higher frequencies.
3. EMI immunity
Another advantage of optical fiber over electrical transmission is that it is immune to electromagnetic interference or electromagnetic interference due to natural and man-made sources such as lighting, solar flares, and radio interference, among others. This advantage makes optical fiber ideal for areas with high levels of electromagnetic interference, such as utilities and power lines.
Note that metal wires are inherently susceptible to electromagnetic interference, while optical fiber is naturally immune to it due to its physical properties. Electromagnetic interference acts on an electrical circuit through electromagnetic induction, electrostatic coupling, or conduction. Interference can degrade the circuit or stop it from working. When transferring data, this can lead to error rates and data loss.
4. Other useful properties of optical fiber
Other useful properties of optical fiber are due to the advantages of fiber optics over electrical wiring or power transmission. For example, because it has a lighter weight and thinner profile than copper wires, it is more ideal for aircraft, restricted paths, or other use cases where heaviness and bulkiness are critical considerations.
Optical fiber is also ideal for combustible or explosive gases because it does not cause sparks, unlike electrical cables. It is also corrosion resistant because it is a non-metallic material. In addition, unlike copper wires, they are also difficult to listen to without interrupting the signal, making it more secure.
Disadvantages of fiber optics
1. More expensive than electrical wires
A remarkable limitation or disadvantage of optical fiber, and hence fiber optic communications, is that it is more expensive to implement or install than electrical transmission systems. This is primarily due to the high cost of optical fiber production.
In addition, optical fibers are more expensive and more difficult to splice and terminate than metal wires. Splicing and termination requires the use of specialized techniques and equipment or materials, requiring a different set of skills than splicing and termination of copper wires.
2. Susceptibility to damage due to fiber fusion
Optical fibers are subject to fiber melting. High optical intensity above two megawatts per square centimeter can lead to fiber burnout, which in turn leads to catastrophic destruction of the optical fiber core and damage to transmission components.
To be more specific, a fuse appears in the heated area of the cable, emitting several watts of light as it travels towards the light sources. Subsequently, this can lead to rapid fiber failure before the fuse trip point.
3.Not suitable for short distances and simpler circuits
Since it is more expensive than copper wires, building a fiber optic infrastructure is not suitable for short distance networks. Remember that a power transmission system is less expensive and has cheaper transmitter and receiver components.
The disadvantages of fiber optics make power transmission more common in smaller applications such as box-to-box, backplane, and chip-to-chip applications. The use of fiber optics on such a scale is impractical, although it has been demonstrated in laboratories.
2. STRUCTURE, EQUIPMENT AND COMPONENTS OF TELECOMMUNICATION SYSTEMS
2.1 Methods and means of measurement in telecommunication systems
Nowadays, network traffic analysis is becoming more and more important and essential for network traffic monitoring. In years past, administrators controlled only a small number of network devices or less than a thousand computers. The network bandwidth could have been slightly less or 100 Mbps (megabits per second). Currently, administrators have to deal with high-speed wired network (over 1 Gb/s (gigabit per second)) and various networks such as ATM (Asynchronous Transfer Mode) network and wireless networks. They require additional advanced network traffic analysis tools to manage the network, quickly resolve network issues to avoid network outages, and ensure network security. Thus, in recent days, the analysis of network traffic presents a number of problems. The network is analyzed at different levels, viz. at the packet level, flow level and network level for security management. Researchers use various methods to analyze network traffic. The general framework for network traffic analysis involves pre-processing followed by actual analysis and observations to identify patterns from network data. Figure 1 shows the three main steps in network traffic analysis. A detailed description of these three steps is provided in the following subsections.
Data set method
Testing and evaluation are important when analyzing network traffic. To evaluate the performance of all research activities using a similar standard list, it is recommended to use a standard data set. Several standard datasets have been used in recent years. We list several important datasets that are used by researchers to analyze network traffic.
Pretreatment Methods
Pre-processing is an important step in using data to transform real data into an understandable format. Undoubtedly, real world data was often incomplete, noisy in certain behaviors. In other words, most of the data we want to analyze from the real world using data mining methods is incomplete and inconsistent (contains errors, outliers). Hence, pre-processing techniques are required before data mining techniques are applied to improve data quality, which helps improve the accuracy and efficiency of the resulting data mining task. Pre-processing techniques are vital and important in network traffic analysis due to network traffic patterns that have different format type and dimension. In the following subsections, we give a detailed description of these methods, which are used in the analysis of network traffic.
Discretization method
Discretization is a pre-processing technique. Discretization is the process of converting continuous attributes into nominal ones. The main goal of the discretization process is to find a set of cut points that divide the range into a small number of intervals. Each cutoff point is a real value in a range of continuous values that divides the range into two intervals, one greater than the cutoff point and one less than or equal to the cutoff point value. Data discretization techniques can be used to reduce the number of continuous attribute values by dividing the attribute’s range into small intervals. Gap labels can be used to replace the actual value of the attributes. Replacing the continuous attribute values with a small number of interval labels reduces and simplifies the original dataset. The sampling process is an important pre-processing technique that reduces network traffic analysis time. Discretization methods can be divided into four categories. (I) Supervised and unsupervised methods Supervised methods use class labels in the discretization process. Unsupervised methods do not use class label information and generate discretization methods by separating numeric attribute values. (II) Global and local methods. The global methods use integer numeric attributes for discretization. However, the local methods use a subset of instances when obtaining a discretization. (III) The top-down (split) and bottom-up (union) top-down (split) discretization methods start with a long as and value interval, then divide the values into smaller intervals at each iteration. However, bottom-up methods start with a basic number of sub-intervals and combine these sub-intervals until the optimal number of intervals is reached. (IV) Direct and incremental methods Direct methods divide a range of values into an equal number of intervals, and users can specify the number of intervals. Incremental methods start with a simple discretization and go through the improvement procedure until a good discretization is obtained, and then stop the discretization process.
Feature selection method
Feature selection (FS) is a pre-processing technique that is applied before data mining techniques are applied. A selection of features used to improve the performance of data mining methods by removing redundant or irrelevant attributes. Feature selection methods generate a new set of attributes by selecting only a subset of the original attributes. Feature selection is mainly used to reduce the dimensionality of the data set to improve the analysis of network traffic. We present various pre-processing methods that are used by researchers before actually analyzing network traffic. We have identified several methods, including Principal Component Analysis, Information Entropy, Approximate Set Theory, Feature Selection, which are often used to preprocess network traffic data.
Data Mining Method
Data mining (DM) is used for knowledge discovery. Data mining plays an important role in network traffic analysis. Our goal is to present various data mining techniques that are used by researchers to analyze network traffic. We have divided data mining methods into four broad categories, namely clustering, classification, hybrid and association rules methods. A detailed description of each method and its use is provided.
Clustering technique
Clustering is the process of dividing data into groups according to certain characteristics of the data. Clustering breaks data into groups of similar objects. Each group, called a cluster, is made up of members that are very similar, and members from different clusters are different from each other.
Clustering methods are used to form groups of network data for network traffic analysis. We have identified that researchers use several data clustering algorithms. Initially, a K-means partitioning algorithm is used to form a network traffic data stream cluster. The corresponding cluster is identified and further split using hierarchical methods to obtain additional clusters. this result of two-section K-Mean clustering is better than pure hierarchical clustering method in terms of traffic analysis.
Scholar Bai Yu, Hong et al. propose an Auto Class clustering data mining tool and K-means algorithms for evaluating the performance impact of wireless mesh networks. The authors collected traffic data from wireless mesh networks that include TCP and UDP over IP. They used the Auto Class tool and the K-means algorithm to classify and identify session clusters. After clustering the log data, racing driven NS-2 models are presented using a mixed wavelet model method to analyze network traffic.
Mixed WM gives better performance for analysis of dependence on wireless mesh networks over long distances. There are three clustering algorithms, K-Means, Auto Class and DBSCAN for classifying network traffic.
It can be noted that the Auto Class algorithm, according to experts, is better suited for classifying network traffic. It also uses K-means clustering data mining method for intrusion detection. They collected a set of data from the MIB network at different time intervals.
The information entropy for selecting the most significant attributes from the entire data set is that four attributes are selected: destination IP address, source IP address, destination port, and source port. Then you need to insert different types of attacks into the network dataset. Next, K-means clustering data mining is used to determine the normal and malicious class. As a result, this approach gave good performance for selecting the best object attributes and high detection accuracy.
2.2 Visualization of the classification of technical means of telecommunication systems.
SNgrep is a unique and very useful tool for analyzing and capturing SIP traffic, building flights and a system of SIP message filters. The purpose of this tool is to make the process of learning or debugging the SIP protocol easier and clearer. SNgrep allows you to display SIP call flows (sip flow) directly in your server console. SNgrep will show SIP messaging in a convenient and readable form. SNgrep is tcpdump (or SNgrep under Linux), but only for VoIP. This utility will be indispensable for VoIP engineers to diagnose telephony systems.
Features:
1-Capture SIP packets from devices or read from PCAP file;
2-Support for UDP, TCP and TLS (partially) transports;
3-Allows you to use BPF (Berkeley Packet Filter) filtering of packets;
4-Save intercepted packets in a PCAP file.
Using SNgrep
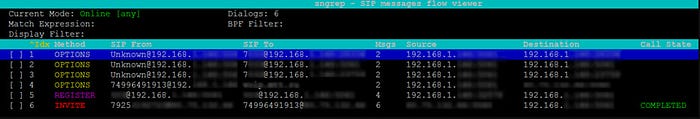
As soon as you get to the utility management menu, a list of VoIP packets that your server processes will be displayed in front of you:
By pressing Enter you will be able to study each message in more detail:
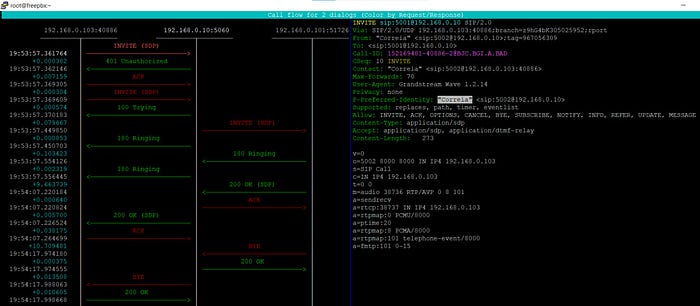
When detailing a call, you can press F2/F3 to get SDR/RTP information.

To exit and return to the previous menu, press Esc. In short, the following options are available in the basic SNgrep interface:
F1 — open the functional assistant;
F2 — save the collected dump to the specified file;
F3 — filter data by the specified row;
F4 — show the selected extended call — flow (the scheme of the call, indicating all the stages of its initiation);
F5 — delete the collected dump;
F6 — show the selected dump in text format (without visualization with arrows, only dry SIP messages);
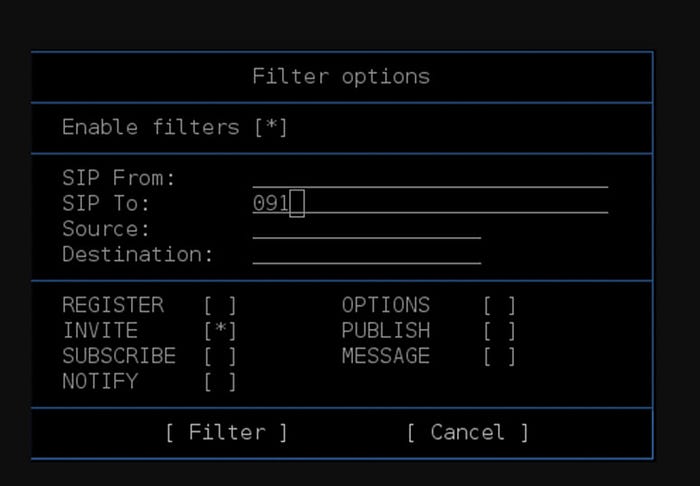
F7 — show filtering options (you can filter by the From/To field, by the source and destination of the call, as well as by various data from the information segment of the payload field, that is, not from the header). Among other things, it is possible to mark message types such as REGISTER, INVITE, OPTIONS and others;
F8 — show settings, including syntax highlighting, background and others;
F10 — setting the displayed parameters (such as From/TO, index, method, and others);
Esc — exit sngrep/to the previous menu;
Enter -view the call-flow of the selected package;
Space (space) — select the desired segment;
i/I — filtering only by INVITE type messages;
p — pause packet collection;
By using the filter system (F7), you can select one or another dialog to analyze and build a trace:
When debugging (diagnosing) an IP telephony service, it is very difficult to analyze VoIP traffic. Is there a more convenient and efficient way to debug VoIP using the SNgrep traffic analyzer program?
The program implements a convenient mechanism for diagnosing (analyzing) VoIP calls, in particular, you can get a graphical diagram of calls and see how data was exchanged. SNgrep allows you to analyze the SIP protocol and its RTP traffic.
Let’s demonstrate this with an example.
Suppose that during a VoIP call using the Grep program, network packets were captured and this dump should be analyzed.
1. Open a previously saved file with a dump of VoIP packets.
2. Select a SIP or RTP packet from the list (in our example, we analyze RTP traffic). To filter packets, you can enter a sip or rtp value in the Filter field to display only a certain type of traffic.
3. You need to go to the Statistics menu (or Telephony, depending on the version of the program) > VoIP Calls. The VoIP Calls window opens with a list of VoIP calls.
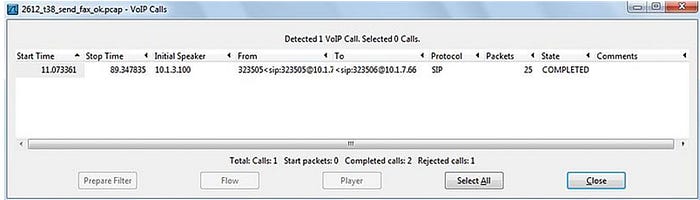
The list of VoIP calls shows the following information for each call:
— Start Time: The start time of the call.
— Stop Time: The end time of the call.
— Initial Speaker: The IP address of the packet source that initiated the call.
— From: For SIP calls, the INVITE request is displayed in the “From” field.
— To: For SIP calls, the INVITE request is displayed in the “To” field.
— Protocol: Protocol.
— Packets: The number of packets participating in the call.
— State: Call status.
— Comment: Additional comments.
4. Select a VoIP call and then click Graph (or Flow, depending on the version of the program). A Graph Analysis window will appear with a graphical diagram of VoIP call data exchange.
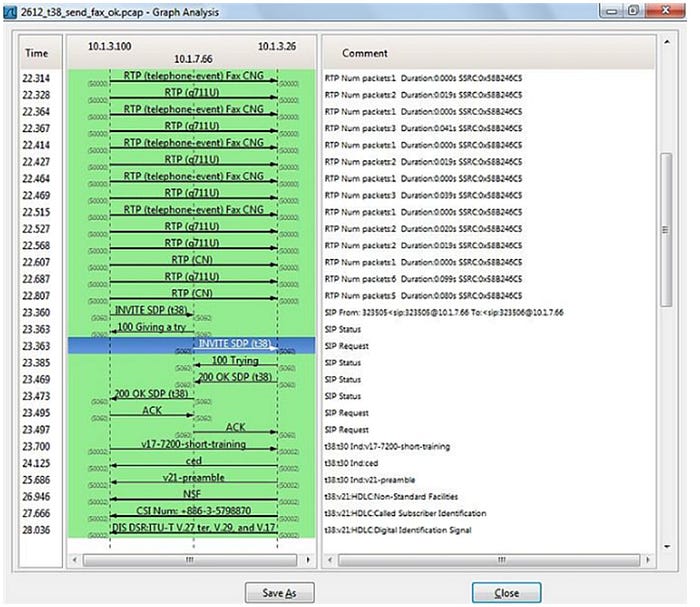
In this diagram, it is much more convenient to analyze VoIP traffic for diagnostics (debugging), but it will require knowledge of the principles of the SIP data transmission protocol (Session Initiation Protocol).
Conclusions: Thus, using the interface of the SNgrep application, it is easy to visualize the classification of technical means of telecommunication systems, namely, tracking the list of VoIP packets.
The modern telecommunications infrastructure provides two fundamentally different types of services: message-oriented and real-time communication-oriented. Examples of messaging-oriented services are file transfer and request-response. Such a service, of course, is implemented through a computer communication network using packet switching. Examples of real-time communications are voice telecommunications and television, which are implemented more naturally over a circuit-switched telephone network (television is broadcast locally, of course, but national programming reaches local stations over permanent circuit-switched connections). However, most services that naturally fit into one of these paradigms are now provided on top of the other to some limited extent.
Since at least 1975, both consumers and telecommunications service providers have dreamed of the day when telecommunications services could be received in a unified way. As the twenty-first century dawns, both packet-switched and circuit-switched networks are ubiquitous, and many believe that this dream of service integration could become a reality within the next few years. Among those who believe that there will be only one telecommunications infrastructure, there are credible opinions based on each technology.
Telecommunication systems, whether packet-switched or circuit-switched, share a number of common elements.
